Admissions
Our team is here to help you choose the right program for your life and your goals.
Speak to Admissions title
title
title
title
title
title
title
title
title
title
title
title
title
title
title
title
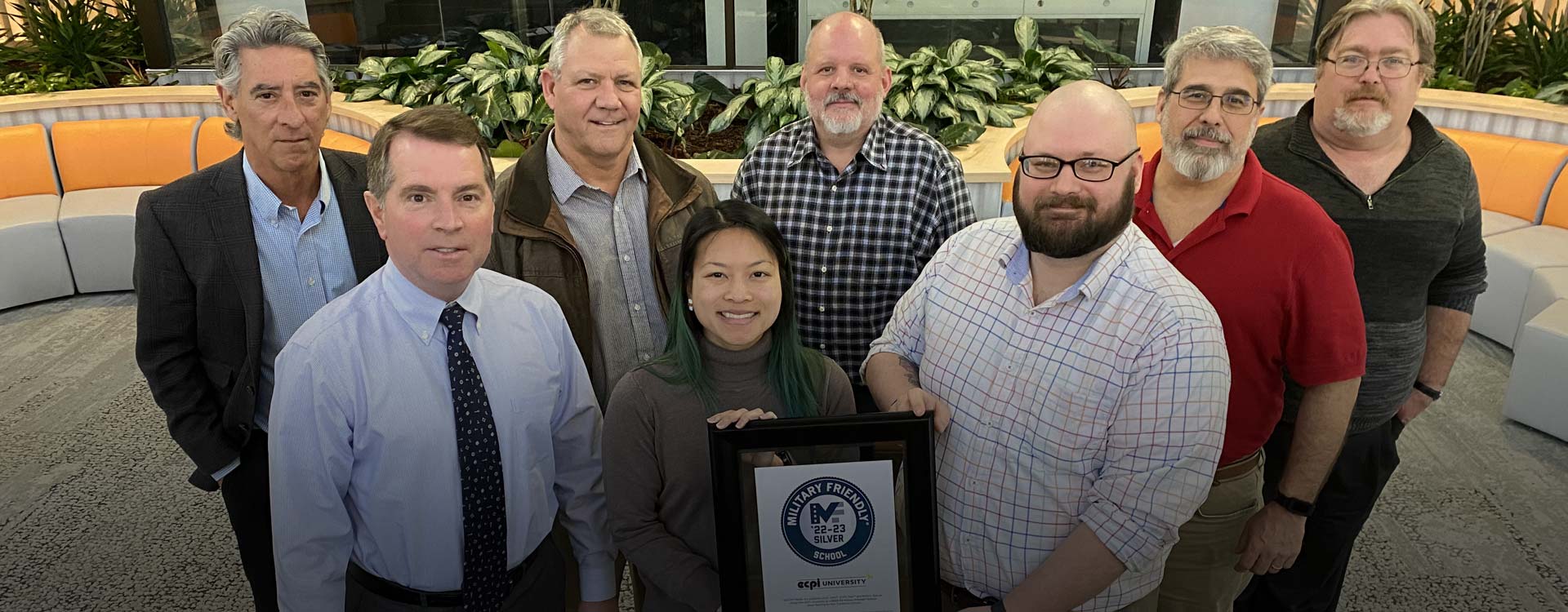
About ECPI University
Founded in 1966, ECPI University promotes a student-centered learning environment as well as personal and professional development through education.
- Program Selectors
- Programs in Technology
- Programs in Nursing
- Programs in Health Science
-
Programs in Business
- Accounting
- Business Analytics
- Business Management
- General Business Management
- Hospitality Management
- IT Management
- Operations, Logistics, and Supply Chain Management
- Human Resources Management
- Leadership
- Project Management
- Master of Business Administration (MBA)
- Master of Human Resources Management
- Master of Organizational Leadership
- Explore Our Business Programs
- Programs in Criminal Justice
- Programs in Culinary Arts
- Campus Locations
- Campus Locations Pt2
Tuition and Financial Assistance
At ECPI University, an affordable education is within reach. Financial assistance options are available to help you invest in your future.