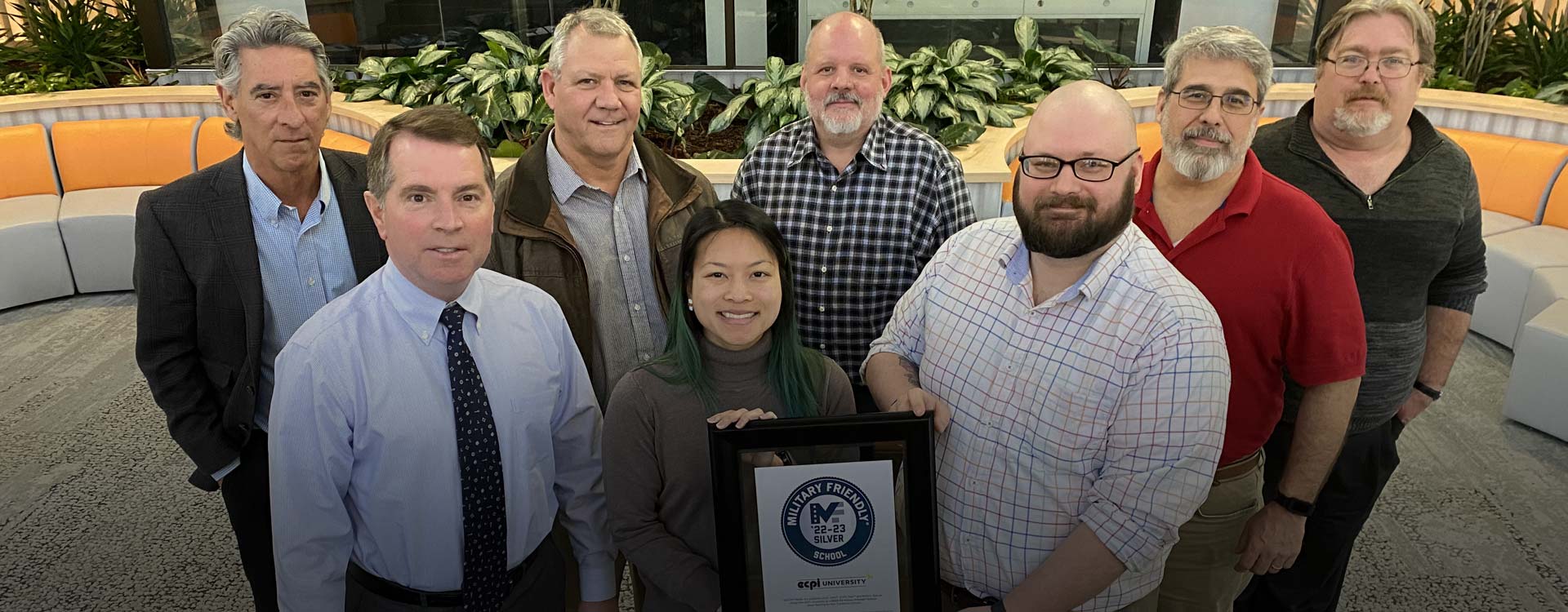
ECPI University Named 2022-23 Military Friendly® School
ECPI University is pleased to announce it has been designated a 2022-23 Military Friendly® School, with a Silver ranking in the Non Traditional Schools category by VIQTORY Media, the publisher of G.I. Jobs, STEM JobsSM and Military Spouse.
ECPI Blog
Learn about our students, programs, and much more.